Gartner SASE MQ 2025 Insight - From Hype to Strategic Control Plane
When SASE first emerged, many enterprise leaders viewed it as a compelling idea wrapped in a healthy dose of hype. That skepticism was understandable. In its early days, SASE often felt more like a future-state vision than a fully realized architecture. Vendors were still stitching together networking and security portfolios, customers were still heavily anchored to legacy firewall and MPLS thinking, and many organizations were not yet operationally ready to consume networking and security as a converged cloud-delivered service.
That has changed.
By 2025, SASE has moved well beyond the hype phase and into a much more meaningful position in enterprise strategy. It is no longer just a conversation about SD-WAN plus cloud security. It is becoming a broader control plane for how organizations connect users, secure access, protect identity, manage data, and increasingly feed security telemetry into more advanced operational and AI-driven workflows.
The most important shift is this: SASE is not standing still. The category is expanding because enterprise environments are expanding. Cloud adoption, SaaS reliance, hybrid work, identity-centric access, AI usage, and the operational strain placed on security teams are all forcing the market to rethink what a SASE platform should actually deliver.
Cato and Palo Alto: Two Different Paths to Leadership
Among the strongest examples of this evolution are Cato Networks and Palo Alto Networks.
Cato continues to represent one of the purest expressions of the original SASE thesis. Its cloud-native, single-pass architecture and tightly integrated platform have helped it stand apart in a market where many competitors still reflect years of acquisition-led product assembly. Cato’s strength comes from clarity: it was built to converge networking and security from the beginning, rather than trying to retrofit that convergence later. That gives it a simplicity and cohesion that continues to resonate with customers looking for operational efficiency and a consistent user experience.
Palo Alto Networks, however, demonstrates a very different but equally important lesson. Scale, brand strength, customer base, and capital still matter. Palo Alto has used those advantages well, rapidly pivoting from a portfolio of powerful but at times separate security technologies into a more unified platform story. In some adjacent areas, particularly around XDR, analytics, and the broader security operations ecosystem, Palo Alto’s maturity can exceed that of more SASE-native players because of the depth and maturity of its overall security business.
This is an important distinction for buyers. Cato may still more closely embody the architectural purity of SASE, but Palo Alto shows how a large incumbent can use platform expansion, strong execution, and adjacent security maturity to compete aggressively and in some cases push beyond the traditional definition of SASE altogether.
SASE Is Expanding Beyond Its Original Boundaries
One of the clearest market developments in 2025 is that SASE is no longer just about connecting branches and securing internet traffic. The leaders are expanding the category into areas that overlap with XDR, identity, AI security, analytics, and operational automation.
That matters because customers no longer think about network and security in cleanly separated terms. They are trying to solve broader challenges: securing remote access, reducing tool sprawl, improving visibility, strengthening identity protection, managing SaaS risk, and responding faster to incidents. As a result, the vendors shaping SASE are increasingly the ones that can provide not only access and inspection, but also deeper context and better operational outcomes.
Cato has steadily expanded its platform beyond the core converged networking and SSE story, including growth in its XDR-oriented capabilities and now a more deliberate focus on AI security. Palo Alto is doing the same from a different angle, tying its SASE evolution into a broader platformization strategy that includes identity, AI security, and security operations.
This is one of the biggest reasons SASE has matured so quickly: it is being pulled forward by customer reality, not just vendor ambition.
SD-WAN Still Matters, But It Is No Longer the Headline
SD-WAN remains foundational to SASE, but it is increasingly table stakes rather than the primary differentiator.
In the early phases of the market, SD-WAN was often the center of the buying discussion. Today, many customers assume that robust WAN capabilities will be present. The real differentiation happens elsewhere: policy consistency, user experience, security depth, operational simplicity, identity integration, data protection, and increasingly how well the platform supports adjacent capabilities such as analytics and threat detection.
That said, SD-WAN is still critically important because it underpins the delivery of the entire SASE experience. Vendors that offer not just distributed PoPs but also some form of meaningful backbone or private global transport tend to deliver more predictable performance. This becomes especially important as SSE converges around ZTNA. ZTNA only works well when users have a reliable and consistent experience. If the underlying transport is inconsistent, then the security model may be sound on paper while frustrating in practice.
In other words, SD-WAN may have become less exciting to talk about, but it remains essential to making SASE actually work.
The Broader Field: Where Vendors Stand Today
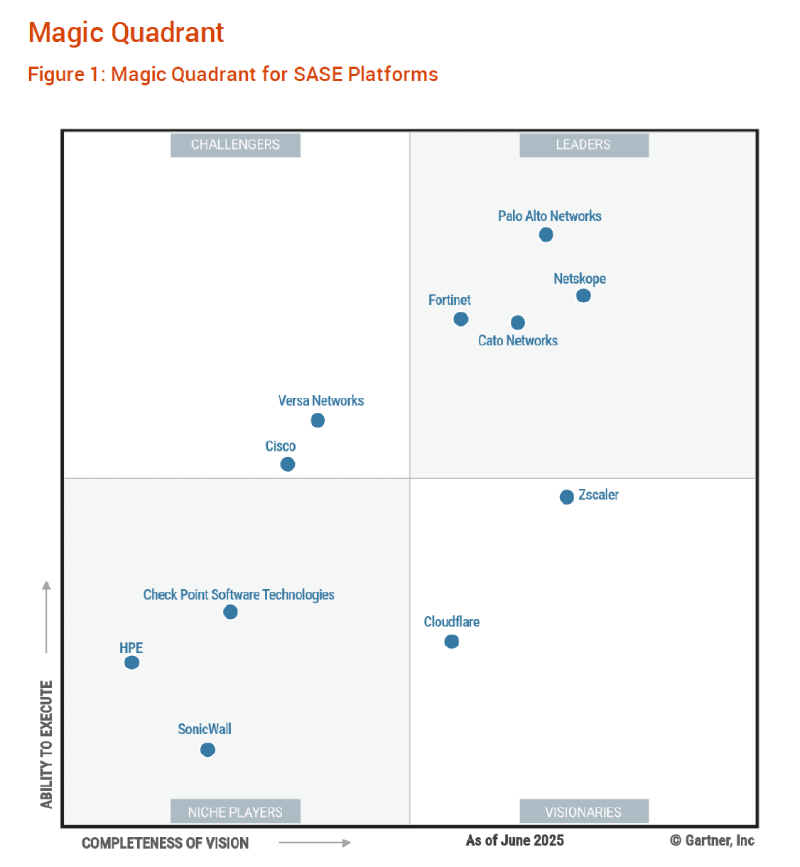
The 2025 landscape makes it clear that the SASE market is no longer a simple race between one or two visionaries. It is now a more layered field with multiple credible players, but also meaningful differences in maturity and positioning.
Fortinet deserves a more balanced read than many market observers give it. While some buyers still see Fortinet primarily through the lens of firewall heritage, the company has clearly earned a place among the top-tier players in the current market. It continues to benefit from deep branch credibility, broad customer familiarity, and a practical migration path for organizations that want to evolve into SASE without fully abandoning their operational roots.
Netskope is another example of a vendor that should not be underestimated. It was once commonly thought of primarily as an SSE or CASB-focused player, but that framing is becoming too narrow. Netskope has expanded its relevance in SASE meaningfully, and while some buyers may still see it as stronger in security than networking, it has moved well beyond being just an SSE specialist.
Cisco remains highly relevant, but it still appears to be pivoting more slowly than the market leaders in terms of architectural simplification. Cisco continues to offer breadth and enterprise familiarity, but many customers still experience the platform as more complex, more bolt-on, and harder to cost-control as they expand into higher-value services such as ZTNA, DLP, CASB, and digital experience monitoring. For some organizations, especially those already deeply invested in Cisco, that may be acceptable. But for others, simplicity and pricing discipline are becoming more important than breadth alone.
Versa remains one of the most interesting vendors in the market. It arguably has some of the strongest technical potential, particularly for organizations with hybrid environments, OT and IoT requirements, or a need for strong on-premises and cloud-delivered controls working together. Versa’s hybrid approach is compelling because it acknowledges that not every customer is ready for a fully cloud-pure model. It also addresses real operational needs around branch security, LAN control, and single-pass inspection. Historically, Versa’s challenge has been less about architectural potential and more about go-to-market execution and customer reach. That continues to affect adoption.
Cloudflare and Zscaler are also important to watch. Both have strong strategic relevance, though for different reasons. Cloudflare benefits from infrastructure scale and a powerful network-first foundation that increasingly supports a broader security and connectivity vision. Zscaler remains especially strong in zero trust and SSE-led transformations and is particularly well positioned where customers want to modernize access aggressively while reducing dependence on legacy VPN models.
HPE and SonicWall continue to face branding challenges as much as product challenges. HPE gained significant opportunity through Silver Peak, but has not fully translated that installed base and potential into a dominant SASE narrative. SonicWall, while advancing, still contends with market perceptions formed during its legacy firewall-heavy era. In both cases, the challenge is not simply building capabilities but convincing buyers that those capabilities now belong in strategic platform conversations.
Why Healthcare and Microsegmentation Matter More Now
Healthcare is one of the best examples of how customer environments are influencing the next phase of SASE.
Hospitals and health systems have historically moved more cautiously than other sectors when adopting new architectures. That caution makes sense. Clinical environments are complex, uptime requirements are unforgiving, legacy infrastructure often lingers longer than expected, and regulatory pressure is constant. But healthcare is also one of the sectors most in need of modernized segmentation, better identity control, and stronger protections against lateral movement.
That is why microsegmentation is becoming more important in the SASE discussion, especially as healthcare security expectations continue to rise. Vendors that can help hospitals move toward a more automated, intelligent, and hybrid-friendly segmentation model may have a meaningful advantage. This is not only about compliance. It is about operationalizing modern security without forcing healthcare organizations into unrealistic transformation timelines.
For hospitals in particular, the appeal of a stronger SASE model is not just secure access. It is the possibility of simplifying a fragmented environment while improving resilience.
Identity Has Become the Center of Gravity
The larger story behind SASE’s evolution is that identity has become the center of gravity in enterprise security.
As organizations continue moving into cloud and SaaS models, the need for heavy edge firewalling has in many cases diminished. Some locations still require strong branch and campus security, of course, especially in manufacturing, healthcare, retail, and distributed enterprise environments. But many organizations are hosting less on premises than they once did, reducing the amount of traditional infrastructure that needs to be protected at the edge.
As that happens, security value shifts toward identity-aware access, endpoint protection, SaaS and cloud security, and the analytics required to detect misuse or compromise quickly. The best operational defenses increasingly focus on making identity compromise harder and more visible. Friction in the identity attack chain remains one of the most effective ways to reduce the impact of modern phishing, session theft, and social engineering.
This is why the expansion of SASE into identity, analytics, and AI security should not be viewed as category drift. It is really the category adapting to where enterprise risk now lives.
Platformization Versus Best of Breed
Over the next few years, one of the defining strategic questions in SASE will be platformization versus best of breed.
The platform approach has obvious benefits. Integrated platforms can reduce operational complexity, improve policy consistency, strengthen shared telemetry, enhance user experience, and create more value from AI and behavioral analytics. Pricing can also be more attractive when multiple functions are delivered through one platform.
But there is another side to the equation. Many larger organizations already have significant investments in endpoint tools, identity providers, SIEM platforms, vulnerability management tools, and cloud security controls. Those enterprises may not want a wholesale platform replacement strategy. They may want better integration more than deeper consolidation.
The vendors that will rise fastest are likely to be the ones that manage this balancing act well. They must provide enough platform cohesion to create operational and economic value, while still integrating cleanly into environments where customers already have strong incumbent tooling and are not ready to rip and replace.
This is not a small issue. It may become one of the most important competitive factors in the market.
Customers Are Driving the Evolution of SASE
It is easy to talk about SASE as though vendors alone are pushing the market forward. In reality, customers are playing just as large a role.
Organizations are changing how they operate. They are moving deeper into SaaS and cloud. They are supporting more distributed workforces. They are contending with rising identity risk. They are experimenting with AI faster than many security teams can comfortably govern it. And they are under continued pressure to reduce complexity while improving resilience.
That means buyers are not simply asking for better network performance or more security features. They are asking for architectures that fit how their business now works.
This is why SASE is gaining relevance. It aligns with the operational reality of modern business. It allows organizations to offload parts of network and security delivery without losing policy control. It supports automation. It reduces dependence on traditional hardware-heavy models. And it gives companies a practical way to simplify environments that were becoming increasingly fragmented.
The Next Few Years Will Be Defining
SASE is no longer just a category born from market hype. It has become a strategic framework for how enterprises deliver secure connectivity, protect users, simplify operations, and increasingly unify adjacent security functions.
But the story is far from finished.
The next phase of the market will likely be shaped by a few major forces: deeper identity integration, stronger AI security capabilities, more intelligent analytics, broader XDR convergence, and continued tension between integrated platforms and open ecosystems.
The vendors that win will not simply be the ones with the largest footprints or the loudest marketing. They will be the ones that can most effectively adapt to how customer environments are changing. That means delivering reliable global connectivity, strong access security, practical operational simplicity, and enough flexibility to meet customers where they are.
SASE began as a bold vision. In 2025, it is becoming a far more complete operating model.
And the most important point for buyers is this: the definition of SASE is still expanding. The vendors, the customers, and the realities of cloud, SaaS, identity, and AI are all reshaping it at the same time.
That is exactly why the next few years will be so important to watch.

